A data breach, from either human error or cyberattack, can give criminals access to the usernames, email addresses, and passwords you use on various online accounts and devices. These credentials, and any data they expose, can then be sold for profit. The selling and buying of this stolen information takes place on the dark web. We’ll look at what the dark web is in a moment, but first understand that credential theft is alarmingly common. While statistics vary, reputable sources from IBM to Symantec put the chance of a business suffering credential theft around 50%, with an even split between hacking and human error.
If you think your business is too small to be a victim of cyber crime, think again. Rather than targeting big corporations and government organizations, criminals often target SMBs due to their less advanced cybersecurity practices. Worse yet, a very high percentage of small businesses do not recover from a data breach, which in 2020 cost an average of $3.86 million per incidence, according to IBM.
But how do criminals get their hands on your details, what do they do with them, and how can you prevent it? We’ll explore all this and more, so that you can protect your business from harm.
How does my email get on the dark web?
Every year, hundreds of millions of accounts are compromised through cyberattacks like phishing, in which criminals send an email posing as a legitimate entity; password spraying, when commonly used passwords are tested against user account names; and credential stuffing, when lists of stolen credentials are entered into multiple accounts in the hope that passwords have been reused. According to Privacy Rights Clearinghouse, more than 11.6 billion records have been breached since 2005.
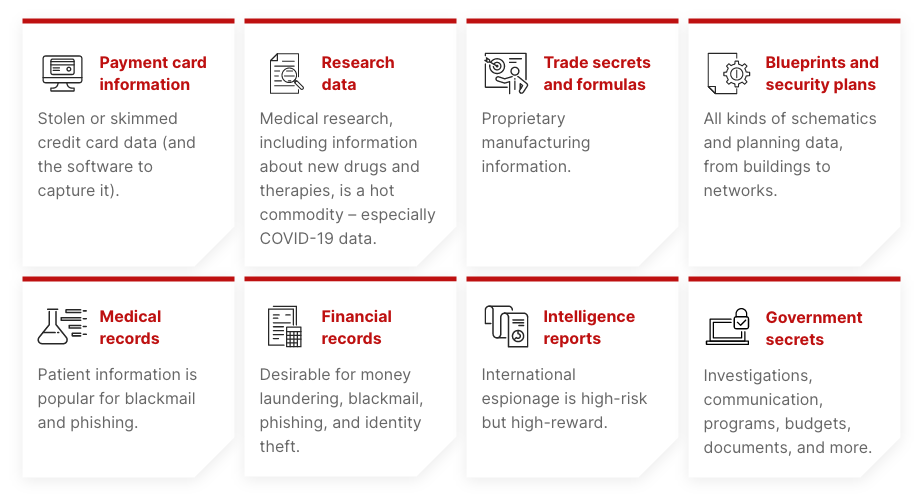
What type of data ends up on the dark web?
How to prevent data from reaching the dark web
Now you’re probably thinking “How do I stop my email from getting on the dark web?” Although it’s impossible to avoid attempted data breaches, you can take the following steps to mitigate risk:
1 – Provide security awareness training
The best cybersecurity in the world is still no match for human error, and it only takes one careless mistake to bring down your business’s entire network. Phishing is the most common technique used by cybercriminals, who pose as potential customers or other trusted entities to persuade victims into entering their credentials or clicking a link. Regular security awareness training enables employees to recognize and report attempted attacks and is far less costly than suffering the effects of a breach.
2 – Up your email security
Your employee email accounts are a gateway for cyber criminals, but you can minimize the chance of malicious mail landing in their inboxes by setting up spam filters. It is also important to maintain up-to-date anti-virus software.
3 – Prioritize strong passwords and MFA
Using weak or common passwords is like ringing the dinner bell for cybercriminals. Never include typical words or phrases like qwerty, password, or 1234 in your password, and definitely don’t use your name or birthday (or the names and birthdays of your family members). A strong password should include a random mix of upper and lower case letters, numbers, and characters.
Never use the same password for multiple accounts because if one of your accounts is hacked, it means all of your accounts can be hacked. Use a different password for every account, and change these passwords frequently. If that sounds like a lot to remember, password managers like LastPass will help.
Also enforce multi-factor authentication (MFA) as an additional layer of security should your password be breached. MFA requires a second credential to be entered after the password, such as a code sent to a smartphone. For more tips, check out our small business security checklist.
A dark web scan: Is my info on the dark web?
One of the most insidious factors with cybercrime today is delayed impact. Most credential thefts or malware attacks remain hidden from view, sometimes for many months. If all this has left you wondering, “is my email on the dark web?”, there’s a simple way to find out. Jasco Technology’s no-obligation dark web scan lets you discover if your email, password, or other sensitive information has been exposed to cybercriminals and identity thieves.
Schedule a scan today and secure the online safety of your business with Jasco. We offer dedicated IT services for your entire business, including comprehensive employee cybersecurity awareness training and cybersecurity plans.

